








Did you do your “auth” well? This is a question that many developers may find themselves pondering. In the rapidly evolving landscape of software development, one critical component of any secure system often overlooked or not fully understood is authentication and authorization. In this article, we will explore how important proper training application security in authentication and authorization is, and the best practices and solutions that can help with these issues.
A concerning trend highlighted by studies, such as the one conducted by TechRepublic, reveals that many developers do not view application security as a top priority. So, what are the reasons?
In software development, inadequate authentication and authorization practices stem from a lack of comprehensive training. Traditional educational institutions and coding bootcamps often prioritize high-level security concepts. They tend to overlook the finer details of authentication and authorization. Many educational programs focus on equipping developers with skills for creating functional applications that meet business requirements. However, they frequently sideline security and compliance essentials.
In the absence of appropriate training, developers may not fully grasp the significance of robust security measures or how to implement them effectively. Consequently, this inadequacy can manifest in software systems characterized by vulnerabilities, ultimately putting user data at risk of compromise.
Learn more: Data Security in the Cloud: Cybersecurity for Cloud-Based Businesses
Many online resources and open-source projects encourage developers to create their own authentication solutions. However, they often lack guidance on implementing proper authorization. Some guides endorse storing user credentials in databases. They may even advocate for weak hashing methods or, in alarming cases, storing passwords in plain text. Authorization’s importance is often downplayed. Some resources prioritize standard authentication behind paywalls, limiting access to crucial information.

Rolling one’s own authentication requires a deep understanding of security best practices and potential vulnerabilities. Without this knowledge, developers might create insecure systems open to exploitation. Additionally, the lack of guidance on authorization implementation leaves developers unsure how to restrict access effectively. This uncertainty can lead to unauthorized access and potential data breaches. Therefore, developers must actively seek comprehensive guidelines and adhere to best practices in authentication and authorization to safeguard their systems’ security.
According to the OWASP Authentication and Access Control guidelines, broken authentication and improper authorization remain among the most critical security risks in modern web applications. Weak password storage, poor token validation, and missing access control checks continue to expose systems to credential stuffing and privilege escalation attacks
The landscape of authentication and authorization has become increasingly complex as security requirements continue to evolve. The rise of Multi-Factor Authentication (MFA) and the gradual shift away from traditional password-based systems have significantly reshaped modern security practices. Many legacy password hashing algorithms are now considered outdated or require careful configuration to remain secure. Yet, some of these weaker methods still persist as defaults in widely used platforms such as WordPress and Drupal.
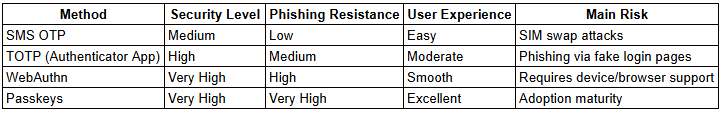
Today, implementing MFA is considered a baseline security requirement. However, the effectiveness of MFA depends heavily on the type of second factor used. While methods like SMS OTP and email-based verification are still common, they are increasingly discouraged due to their susceptibility to phishing and SIM-swap attacks.
At the same time, more advanced and phishing-resistant standards such as WebAuthn are gaining traction. Even more transformative are passkeys, which move beyond the traditional username-and-password model altogether. By leveraging public-key cryptography and device-based authentication, passkeys represent a fundamental shift toward more secure and user-friendly digital access.
Industry data reflects this transition. Organizations are rapidly adopting passwordless authentication to reduce phishing risks and credential-based attacks. Security experts now widely agree that traditional MFA methods alone are no longer sufficient to defend against sophisticated phishing techniques. As a result, the industry is steadily moving toward phishing-resistant authentication standards such as WebAuthn and passkeys.
2.2. Key Insights:
For organizations handling financial data, healthcare information, or SaaS platforms, transitioning toward phishing-resistant authentication is increasingly becoming best practice.
Fortunately, there are now well-established standards for authentication and authorization. These standards make life easier for developers and enhance security across the digital landscape. OpenID Connect and OAuth 2 have emerged as the go-to standards adopted by a multitude of medium to large international companies. These standards offer mature user experiences and impeccably designed workflows that cater to a wide array of environments. With robust authentication mechanisms and streamlined authorization processes, these standards have become the backbone of modern identity management.
Additionally, authorization approaches such as Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) aren’t universally standardized. However, many systems and applications widely embrace them. Developers have access to numerous proprietary and open-source solutions. These solutions have substantial user bases, mature products, and accessible documentation. Recognized names such as Auth0 and Ping Identity offer powerful tools and comprehensive documentation. Consequently, they are the preferred choice for numerous prominent enterprises. Simultaneously, open-source alternatives like Keycloak and Authelia have gained popularity for their robust feature sets and well-documented capabilities. Furthermore, major frameworks such as .NET and Spring have built-in support for OpenID Connect and OAuth 2. They provide developers with a wealth of options and reducing the need to reinvent the wheel when implementing authentication and authorization systems. This array of choices empowers developers to select the most suitable solution for their specific needs, saving valuable time and ensuring robust security measures.
Learn more: Shielding Your Apps: Secure Mobile App Development for Uncompromised User Data
Authentication and authorization are integral components of secure software development. While the lack of training and awareness has led to vulnerabilities in many applications, the landscape is evolving with new standards and solutions. Developers should prioritize security, adopt best practices, and leverage available tools to protect their applications and users.
At ITC, as an ISO 27001:2013 certified company with extensive experience and knowledge in building secure products, we are well-equipped to help companies navigate these challenges and deliver secure solutions. With our expertise in popular tools like Azure AD, AWS Cognito, and Keycloak, we have successfully delivered products for numerous companies, including Selz, UpDiagram, ACB, FE Credit and are committed to ensuring the highest level of security for your projects.
WebAuthn (Web Authentication API) is a modern authentication standard that enables passwordless and phishing-resistant login. Instead of relying on traditional passwords, WebAuthn uses public-key cryptography to authenticate users through biometrics, hardware security keys, or trusted devices. It significantly reduces the risk of credential theft and phishing attacks.
Authentication verifies who a user is, while authorization determines what that user is allowed to do.
For example, logging into an application is authentication. Accessing admin-level settings or restricted data is authorization. Both must be implemented correctly to ensure secure application access.
RBAC (Role-Based Access Control) assigns permissions based on predefined user roles, making it simpler and easier to manage.
ABAC (Attribute-Based Access Control) grants access based on multiple attributes such as user type, department, location, device, or time of access.
RBAC is ideal for straightforward systems, while ABAC provides greater flexibility and fine-grained control in complex environments.
Organizations should consider adopting passkeys when they want to improve both security and user experience. Passkeys eliminate passwords entirely and are resistant to phishing attacks.
They are especially beneficial for SaaS platforms, financial applications, healthcare systems, and any environment handling sensitive user data.
Traditional MFA methods such as SMS-based OTP improve security compared to passwords alone, but they are not fully resistant to phishing and SIM-swap attacks.
Modern best practice is to implement phishing-resistant authentication methods such as WebAuthn or passkeys, especially for high-risk or regulated systems.
Stay ahead in a rapidly changing world with our monthly look at the critical challenges confronting businesses on a global scale, sent straight to your inbox.